Online code repository GitHub continues to face a distributed denial-of-service (DDoS) attack on Monday, which the company reported is the largest attack in GitHub.com’s history. The attack began on Thursday and still continues, according to GitHub’s status page and Twitter accounts,
though the company says now that all its systems are reporting at 100%.
However, the attackers continue to evolve their methodology as the
barrage continues, requiring GitHub to remain on “high alert,” it says.
Online code repository GitHub continues to face a distributed denial-of-service (DDoS) attack on Monday, which the company reported is the largest attack in GitHub.com’s history. The attack began on Thursday and still continues, according to GitHub’s status page and Twitter accounts,
though the company says now that all its systems are reporting at 100%.
However, the attackers continue to evolve their methodology as the
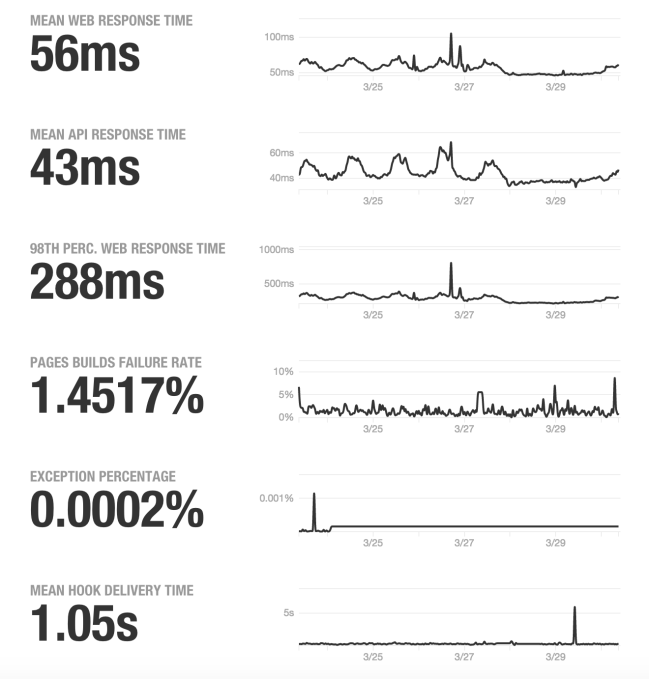
barrage continues, requiring GitHub to remain on “high alert,” it says.In a blog post from last week, GitHub said there were a number of vectors being used in this attack, including some new and sophisticated techniques that involved using the web browsers of unsuspecting users to flood the GitHub site with traffic. This traffic flood led to reduced availability of GitHub’s systems, as you can tell by the historical graphs on GitHub’s status page, which shows spikes of activity over the past several days.
Specifically, security experts report that the attackers were redirecting search traffic from overseas users of the Chinese search engine Baidu, and were targeting two pages in particular. One page was run by Greatfire.org, a site that reports on the government censorship in China, and the other linked to a copy of the New York Times’ Chinese language website. The Greatfire-run page linked to copies of 10 websites blocked in China. Of note, that organization suffered from a DDoS of its own earlier this month.
While GitHub didn’t confirm which pages were under attack, it did say in its blog post that: “based on reports we’ve received, we believe the intent of this attack is to convince us to remove a specific class of content.”
Security experts told The WSJ that the attack appeared to be linked to Chinese authorities because the hackers were able to manipulate the traffic at a high level of China’s internet infrastructure, meaning it had to come from someone who had the ability to tamper with all the traffic coming into the country.